Trust is a key part of our company's value. Our goal is to minimize risk and keep customers secure while they conduct transactions on our platform.
The pandemic has led people to switch from traditional payment solutions to online ones. However, with the increased reliance on digital financial solutions, the sector is now more susceptible to cybercrimes.
According to the 2022 IBM Security X-Force Threat Intelligence Index, 60% of cyberattacks in 2021 targeted financial services and manufacturing organizations in Asia.
At the same time, there are more and more sophisticated cyberattacks in 2022 than ever. Criminals have grown more resourceful and sophisticated, relying less on social engineering techniques like phishing emails and phone-based fraud.
Instead, they are now utilizing more malware and new emerging technologies. The malware used by hackers has changed and become more dangerous, and ransomware has become one of the biggest cyber threats.
We value our customers’ trust in us, and we want to go above and beyond to keep their money safe.
That’s why we are implementing new technologies to improve our cybersecurity and the peace of mind of our customers.
One measure we are using is called Multi-factor authentication (MFA).
User notice:
Here is a step-by-step guide to help you adopt MFA as smoothly and easily as possible.
Next, we will try to cover the basics.
What is MFA?
Multifactor authentication is a security technique and set of technologies that use two or more independent categories of credentials and security steps to verify the user’s identity for a login or other transaction.
The three most common categories or authentication factors include the knowledge factor or using secrets that a person knows such as the common pin or user name and password combination ; the possession factor or something that person has, like a physical security token; or the inherence factor that is something unique and unchanging about them, like fingerprints, which is called biometrics.
MFA creates a layered defense that makes it more difficult for unauthorized persons to access a target, such as a physical location, computer, network, or database. If one layer of protection is compromised or broken, the attacker still has at least one or more barriers to breach before successfully breaking into the target.
How Does MFA Work?
The most common multi-factor authentication systems still use passwords but add at least one other factor and additional step before letting someone into an account.
Each of these factors has its own strengths and considerations when used for security:
● SMS, the short message system, is the text messaging service component of mobile telephone service, which uses standardized communication protocols. Used for MFA, the system sends you a temporary code in a text message to enter into the site or app. This means that you have to have your mobile device to get to the site.
● Emails used for MFA are just like SMS text messages, with a temporary code or password. This requires you to have access to the email account that you used to sign up for the service.
● Voice calls are generally handled by an automated system that gives you instructions to follow and questions to answer. This often requires a piece of private information in addition to using the phone number associated with your account.
● Mobile apps are as secure as the people who write, maintain, and support them and the underlying technologies chosen. A mobile application developed with security in mind, with good people behind it, is one of the most secure factor options available in 2022.
● Universal 2nd Factor (U2F) security keys are physical items like USB sticks. The item holds additional cryptographic information designed to be a good second authentication factor.
● Physical one-time PIN (OTP) tokens are physical devices capable of producing a one-time-use code, pin, or password. These tokens use complex cryptographic algorithms. Sometimes they are also called dynamic passwords. The acronym OTP is not to be confused with “One Time Pad”, which is an older security scheme.
● Biometrics use unchanging physical features, such as your thumbprint. Biometrics are convenient, but can’t be changed.
● Smart Cards have a smart chip in them and look like a credit card. Also like a credit card, they work by being inserted into a reader or using an NFC chip. They are usually used with a PIN. Smart cards can be made to the highest security standards, and are very difficult to defeat.
● Software certificates typically use public-private key encryption schemes, have expiration dates, and are usually signed by an authority with a secret key that issues such certificates. This makes them additionally trustworthy. They can be tied to your identity, or at least the identity of a device you own, and they are also frequently used to secure websites and software updates.
MFA at Statrys
Why Passwords Just Aren’t Enough Anymore
Passwords can provide very good security if chosen well, but simply are not good enough protection for your important accounts on their own. That’s true even if you use a strong, unique password for every account.
The criteria for a strong password are that it should be long, memorable, and contain upper and lower case letters, numbers, and special characters. Unfortunately, even strong passwords can also be guessed, shared, stolen, or forgotten.
Password managers can be hard to trust because they create a single point of failure. If a password manager is compromised, then all the accounts for which it holds passwords will be compromised as well.
In short, passwords just don’t provide enough security on their own, even if they are strong.
Taking Security to a Whole New Level
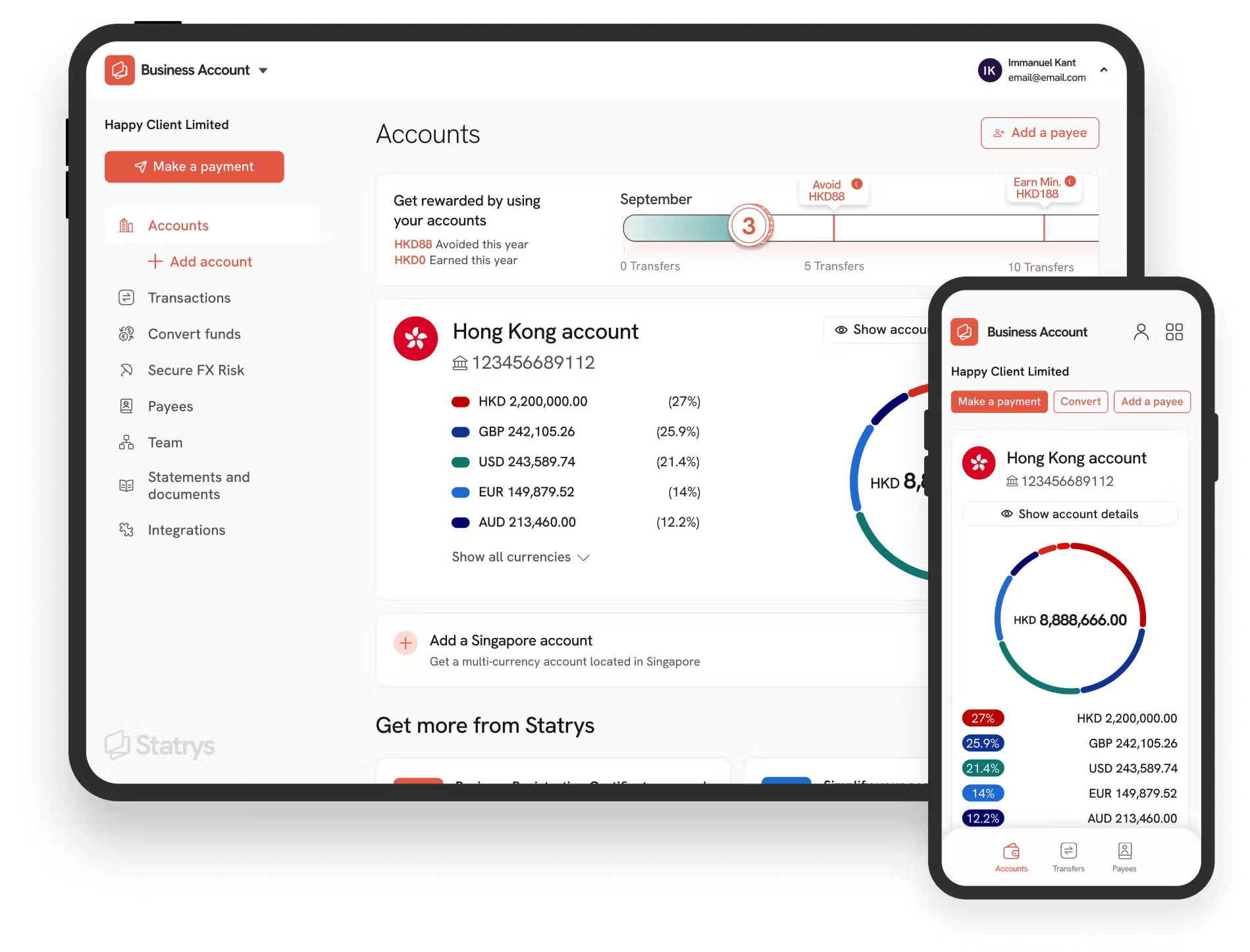
We are now using multi-factor authentication at all levels of our platform and mobile app. With this, we want to reinforce the security by looking at these 3 components:
- Is this really the user and can they be trusted?
We want to make sure our customers can access their accounts easily without having to worry about someone stealing or hacking their password.
- Can users’ devices and networks be trusted?
We're building a digital profile of our customers by tracking their behavior on our site. Each transaction, mobile device, and new address contributes to the profile and helps us understand who they are and how they normally transact.
- Are there any viruses, spyware, or other malware in effect?
We’re on the lookout for suspicious programs that may infiltrate a device without the owner’s knowledge. With the user’s digital profile, we can determine if it's the user or a bad actor who is compromising their account using malicious software.
Logging into Statrys account with MFA
At Statrys, we’ll ask 2 different factors to authenticate users' identities.
Each time users access their Statrys business account, besides their login and password, they will need to confirm their identity via either:
- an SMS sent to their mobile phone number
- or tapping "Confirm" on the Statrys Mobile app
We've prepared a step-by-step guide to help our users to adopt MFA as smoothly and easily as possible.
Final note
Using these extra steps for multi-factor authentication is much safer and more secure for customer accounts and any monetary transactions.
We take cybersecurity very seriously, and keeping your data and money safe is very important to us.